http://www.portablefreeware.com/index.php?id=2713
100% Stealth portable AFAICT.
What is the detection name, or the reason given?JohnW wrote:Avast blocks the download.
Avast is prone to false positives on portable versions of standard software. Normally OK on standard freeware
Suggest you resolve this somehow
Avast Web Shield blocks it; DRep (DomainRep).flatfly wrote:Thanks for checking!
What kind of warning do you get?
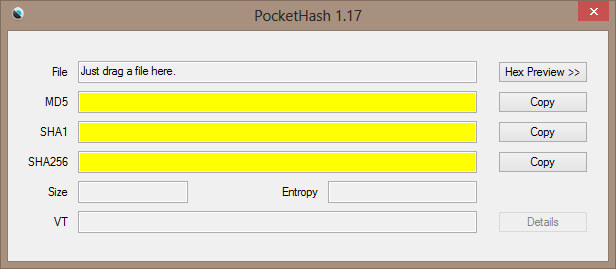
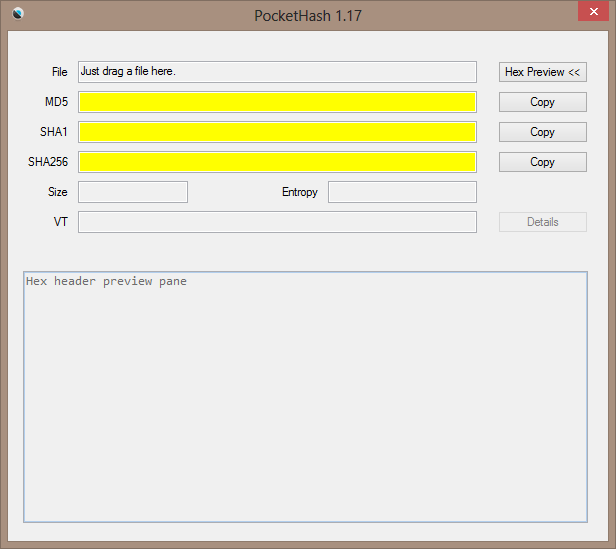
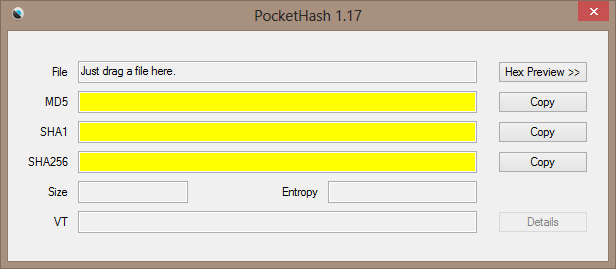
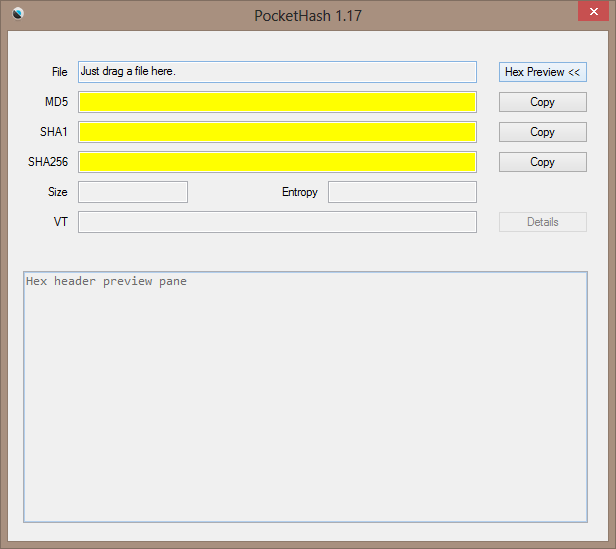
The next version will look something like this (and will support SHA-256 as well). Does that look better to you?I am Baas wrote:Please consider removing the link that "opens the homepage of PocketHash."

Looks good. Can I also make a few suggestions?flatfly wrote:Does that look better to you?
Hash function security matters only if you're concerned about the possibility that someone has intentionally replaced the file with something malicious but retained the hash (which, AFAIK, is only a theoretical possibility, and no one has actually carried out such an attack in the wild). If you're only checking if the file has corrupted during the download, MD5 or even CRC32 is fine.Midas wrote: ↑Sat Jun 23, 2018 4:57 am Regarding webfork's doubts on the best choice of hashing standards, let me refer back to Wikipedia's article on "Hash function security summary", based on which I advocate that crc32, md5 and SHA-1 must be retained for historical reasons, but that SHA256 is now the absolute baseline for anyone concerned with this.
Agreed. As useful as VirusTotal checks are, it's ideal to make them available but disabled by default. An increasing number of connection points are used by Google, so just submitting them outside adds to a user profile.
Agreed. Corruption checks are fairly easy for computers and even ancient algorithms (like CRC32) are more than adequate. It's that files can be crafted by computers to appear legitimate is the major threat and really only SHA-256 is (currently) considered safe.
Midas wrote: ↑Since we're debating this, the ability to write a specific hash directly to file in a standard fashion is my foremost requirement.