Did you actually research into those entries? I fail to see how these keys affect stealthness, please educate me.SYSTEM wrote:Thanks. Based on that information, QIcon Changer is portable but not stealth. I have edited the entry.ajfudge wrote: QIcon Changer (extracted via UniExtract) with analysis using Sandboxie and Buster Sandbox Analyzer.
I don't understand reg entries, so anyone who does might find this helpful.
QIcon Changer [& PE Icon Changer]
Re: QIcon Changer v1.0
Re: QIcon Changer v1.0
I don't recall stealth applications modifying these keys (other than MUICache). That's all.I am Baas wrote:Did you actually research into those entries? I fail to see how these keys affect stealthness, please educate me.SYSTEM wrote: Thanks. Based on that information, QIcon Changer is portable but not stealth. I have edited the entry.
My YouTube channel | Release date of my 13th playlist: August 24, 2020
- loin2kolpotoru
- Posts: 279
- Joined: Fri Oct 09, 2009 11:20 am
Re: QIcon Changer v1.0
What is the difference between portable & stealth?
Re: QIcon Changer v1.0
There is no exact definition for portability. There is some discussion in http://www.portablefreeware.com/about.php.loin2kolpotoru wrote:What is the difference between portable & stealth?
Stealth is a subset of portable. It is defined in http://www.portablefreeware.com/faq.php#stealth.
My YouTube channel | Release date of my 13th playlist: August 24, 2020
- Andrew Lee
- Posts: 3063
- Joined: Sat Feb 04, 2006 9:19 am
- Contact:
Re: QIcon Changer v1.0
At I am Baas' request, I run a test on QIcon using regshot. Here's my result:
Doesn't appear to actively modify the registry.
In ajfudge's report, the changes made to "HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Explorer" are system related and cannot be attributed to the application.
So the only suspicious entries are:
which I was unable to replicate.
Hopefully someone else can test using another method to verify.
Code: Select all
----------------------------------
Values added:1
----------------------------------
HKU\S-1-5-21-789336058-839522115-725345543-1000\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{75048700-EF1F-11D0-9888-006097DEACF9}\Count\HRZR_EHACNGU:P:\Grzc\DVpbaPunatre.rkr: 87 00 00 00 06 00 00 00 D0 A4 F4 96 8E 14 CE 01
----------------------------------
Values modified:2
----------------------------------
HKLM\SOFTWARE\Microsoft\Cryptography\RNG\Seed: 1D B9 EC 97 35 44 E9 28 EA B6 9E 15 A6 45 26 40 71 8F C9 0D 59 7C 92 21 32 30 08 31 FC E6 17 A6 B8 D7 F5 91 DF 6C B7 4E 77 52 FB 2C 17 5A A8 4F 1A 31 27 A6 4F 68 06 B4 F2 5A E8 6F 07 78 CC 2C DB 3F 5F 8F 15 05 60 CB D3 B2 5C E1 A8 35 66 C5
HKLM\SOFTWARE\Microsoft\Cryptography\RNG\Seed: 0E 34 F2 C6 6D 2C A4 47 37 13 12 A5 FC 0A 37 B9 4E 56 47 21 0B 28 04 DE 5C D8 E4 9C 45 ED 5C 03 89 27 17 48 D3 9F CD F5 F3 1F 95 68 FB A9 40 17 AA 50 A7 40 C4 00 01 B9 0C 27 29 65 DF 77 33 F0 C2 07 B9 49 D0 64 59 78 8E 52 D2 5E 25 81 F7 7B
HKU\S-1-5-21-789336058-839522115-725345543-1000\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{75048700-EF1F-11D0-9888-006097DEACF9}\Count\HRZR_EHACNGU: 87 00 00 00 7D 05 00 00 C0 30 04 93 8E 14 CE 01
HKU\S-1-5-21-789336058-839522115-725345543-1000\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{75048700-EF1F-11D0-9888-006097DEACF9}\Count\HRZR_EHACNGU: 87 00 00 00 7E 05 00 00 D0 A4 F4 96 8E 14 CE 01
----------------------------------
Files [attributes?] modified:6
----------------------------------
C:\WINNT\system32\config\SAM
C:\WINNT\system32\config\SAM.LOG
C:\WINNT\system32\config\software
C:\WINNT\system32\config\SOFTWARE.LOG
C:\Documents and Settings\User\NTUSER.DAT
C:\Documents and Settings\User\ntuser.dat.LOGIn ajfudge's report, the changes made to "HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Explorer" are system related and cannot be attributed to the application.
So the only suspicious entries are:
Code: Select all
* Creates Registry key HKEY_LOCAL_MACHINE\software\classes\clsid\{1F486A52-3CB1-48FD-8F50-B8DC300D9F9D}
* Creates Registry key HKEY_LOCAL_MACHINE\software\microsoft\SQMClient\WindowsHopefully someone else can test using another method to verify.
Re: QIcon Changer v1.0
Thank you for the reaffirming QIcon status, Andrew. Much appreciated.Andrew Lee wrote:Hopefully someone else can test using another method to verify.
Btw, did you test it "sandboxed"?
PE Icon Changer
Last edited by I am Baas on Fri Oct 04, 2013 7:33 pm, edited 1 time in total.
Re: QIcon Changer v1.0
Status update:
QIcon Changer direct Phrozensoft blog download page: http://phrozenblog.com/?p=6.ps.
QIcon Changer download sources and discrepancies observations remain valid.
QIcon Changer direct Phrozensoft blog download page: http://phrozenblog.com/?p=6.ps.
QIcon Changer download sources and discrepancies observations remain valid.
- Softpedia "QIcon Changer.exe": 1 934 848 Bytes, dated 2012-03-13 (PEStudio report @ http://pastebin.com/23x85Y8A).
- Phrozenblog "QIconChanger.exe": 1 604 608 Bytes, dated 2012-07-29 (PEStudio report @ http://pastebin.com/U0Sp2b1u).
- (Diff results @ http://pastebin.com/Zy1TAAEz)
ajfudge wrote:Here's a list of actions made by QIcon.[...] [ Changes to registry ]
* Creates Registry key HKEY_LOCAL_MACHINE\software\classes\clsid\{1F486A52-3CB1-48FD-8F50-B8DC300D9F9D}
* Creates Registry key HKEY_LOCAL_MACHINE\software\microsoft\SQMClient\Windows
* Modifies value "NukeOnDelete=00000001" in key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Explorer\BitBucket\Volume\{871b19f7-7348-11e2-846c-806e6f6e6963}
old value empty
* Modifies value "NukeOnDelete=00000001" in key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Explorer\BitBucket\Volume\{871b19f8-7348-11e2-846c-806e6f6e6963}
old value empty
* Modifies value "NukeOnDelete=00000001" in key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Explorer\BitBucket\Volume\{871b19f9-7348-11e2-846c-806e6f6e6963}
old value empty
* Modifies value "NukeOnDelete=00000001" in key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Explorer\BitBucket\Volume\{871b1a13-7348-11e2-846c-806e6f6e6963}
old value empty
* Modifies value "NukeOnDelete=00000001" in key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Explorer\BitBucket\Volume\{871b1a14-7348-11e2-846c-806e6f6e6963}
old value empty
* Modifies value "NukeOnDelete=00000001" in key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Explorer\BitBucket\Volume\{871b1a15-7348-11e2-846c-806e6f6e6963}
old value empty
* Empties value "_CommentFromDesktopINI" in key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\{871b19f8-7348-11e2-846c-806e6f6e6963}
old value "_CommentFromDesktopINI=0000"
* Empties value "_CommentFromDesktopINI" in key HKEY_CURRENT_USER\software\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\{871b19f9-7348-11e2-846c-806e6f6e6963}
old value "_CommentFromDesktopINI=0000"
* Creates value "QIconChanger.exe=QIconChanger.exe" in key HKEY_CURRENT_USER\software\classes\Local Settings\Software\Microsoft\Windows\Shell\MuiCache\D:\Station\Apps\DE\DESKSTYLE\ICON STYLES\ICON CHANGER\QIcon 1.0\{app}
binary data=5100490063006F006E004300680061006E006700650072002E006500780065000000[/quote
Re: QIcon Changer v1.0
QIcon Changer - 2012.03.13
QIcon Changer - 2012.07.29
DarkCoderSC is the author of the infamous DarkComet RAT - (malware analysis by Context Information Security)
I traced the early version of QIcon Changer back to his Google+ post HERE
His announcement of PhrozenBlog HERE
I believe he was slowly disassociating his handle with his 'legit' apps as can be evidenced by the creation of his blog HERE and subsequent removal/discontinuance of DarkComet in this post HERE
DarkComet Surfaced in the Targeted Attacks in Syrian Conflict
http://blog.trendmicro.com/trendlabs-se ... -conflict/
The End of DarkComet RAT
http://www.cybercrimereview.com/2012/07 ... art-1.html
An interesting note about DC RAT HERE
Spoiler!
Spoiler!
I traced the early version of QIcon Changer back to his Google+ post HERE
His announcement of PhrozenBlog HERE
I believe he was slowly disassociating his handle with his 'legit' apps as can be evidenced by the creation of his blog HERE and subsequent removal/discontinuance of DarkComet in this post HERE
DarkComet Surfaced in the Targeted Attacks in Syrian Conflict
http://blog.trendmicro.com/trendlabs-se ... -conflict/
The End of DarkComet RAT
http://www.cybercrimereview.com/2012/07 ... art-1.html
An interesting note about DC RAT HERE
~RubyDarkComet RAT is maybe one of the biggest Delphi project in the world with more than 3000 source files; 35 Window Forms and more than 150Mo of code. All the potential of Delphi is used in this project.
Re: QIcon Changer v1.0
Thanks, Ruby. It all used to be on unremote.se. DarkComet RAT is now hosted at http://unremote.org/ and other apps on PhrozenSoft Blog.
Re: QIcon Changer v1.0
A correction:Ruby wrote: The End of DarkComet RAT
http://www.cybercrimereview.com/2012/07 ... art-1.html
VirusTotal submits samples it has obtained to AV vendors. AFAIK, crackers (not hackers) avoid VirusTotal like the plague.Justin P. Webb wrote: Hackers will often test their newly packed versions against VirusTotal - a site which runs a binary through a multitude of anti-virus products, and reports whether or not it is picked up. The holy grail is 0/40, aka undetectable - and this is even taking account of the heuristics and "learning" that AV vendors claim to have injected into their detection engines.
Whois data shows that unremote.org belongs to DarkCoderSC: [Moderator note: Link to whoisxmlapi.com removed at their request].I am Baas wrote:Thanks, Ruby. It all used to be on unremote.se. DarkComet RAT is now hosted at http://unremote.org/ and other apps on PhrozenSoft Blog.
My YouTube channel | Release date of my 13th playlist: August 24, 2020
Re: QIcon Changer v1.0
Cool piece of Internet archaeology there, SYSTEM -- it immediately reminded me of another much maligned software tool, the zanily called Low Orbit Ion Cannon (https://en.wikipedia.org/wiki/Low_Orbit_Ion_Cannon). 
Back to OT, I guess it can now be safely assumed that QIcon Changer is both portable and stealth, and better yet malware free?
BTW, recent Virustotal.com results are at:
Back to OT, I guess it can now be safely assumed that QIcon Changer is both portable and stealth, and better yet malware free?
BTW, recent Virustotal.com results are at:
- loin2kolpotoru
- Posts: 279
- Joined: Fri Oct 09, 2009 11:20 am
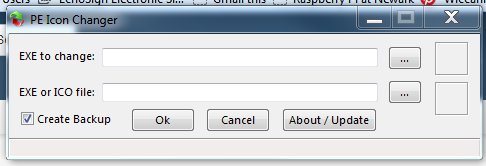
PE Icon Changer
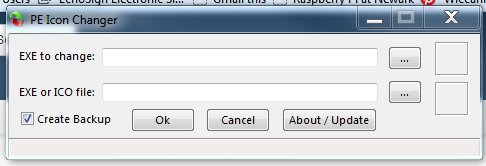
PE Icon Changer allows the user to change the main icon of an EXE file.
http://starpunch.blogspot.com/2013/03/P ... anger.html
It is better then QIconChanger because it supports importing icon from exe files which QIconChanger dose not support
Re: PE Icon Changer
PE Icon Changer has been mentioned before by I am Baas -- viewtopic.php?p=62750#p62750.
Re: PE Icon Changer
No prob - merged.Midas wrote:PE Icon Changer has been mentioned before by I am Baas -- viewtopic.php?p=62750#p62750.